
호환 APK 다운로드
| 다운로드 | 개발자 | 평점 | 리뷰 |
|---|---|---|---|
|
Security Breach 4K Wallpapers 다운로드 Apk Playstore 다운로드 → |
mkangchul04 | 4.3 | 83 |
|
Security Breach 4K Wallpapers 다운로드 APK |
mkangchul04 | 4.3 | 83 |
|
Security Squid : Breach Game 다운로드 APK |
FRONS ENT | 3 | 100 |
|
FNaF 9 : Security breach Mod 다운로드 APK |
ROYADOLPHIGAME.INC | 3 | 100 |
|
Gregory FNAF Security Breach 다운로드 APK |
Carrie Apps | 2.1 | 91 |
|
Security Breach X Ruin Video 다운로드 APK |
GreenDev Ltd | 3 | 100 |
다른 한편에서는 원활한 경험을하려면 파일을 장치에 다운로드 한 후 파일을 사용하는 방법을 알아야합니다. APK 파일은 Android 앱의 원시 파일이며 Android 패키지 키트를 의미합니다. 모바일 앱 배포 및 설치를 위해 Android 운영 체제에서 사용하는 패키지 파일 형식입니다.
네 가지 간단한 단계에서 사용 방법을 알려 드리겠습니다. Security Breach Monitoring 귀하의 전화 번호.
아래의 다운로드 미러를 사용하여 지금 당장이 작업을 수행 할 수 있습니다. 그것의 99 % 보장 . 컴퓨터에서 파일을 다운로드하는 경우, 그것을 안드로이드 장치로 옮기십시오.
설치하려면 Security Breach Monitoring 타사 응용 프로그램이 현재 설치 소스로 활성화되어 있는지 확인해야합니다. 메뉴 > 설정 > 보안> 으로 이동하여 알 수없는 소스 를 선택하여 휴대 전화가 Google Play 스토어 이외의 소스에서 앱을 설치하도록 허용하십시오.
이제 위치를 찾으십시오 Security Breach Monitoring 방금 다운로드 한 파일입니다.
일단 당신이 Security Breach Monitoring 파일을 클릭하면 일반 설치 프로세스가 시작됩니다. 메시지가 나타나면 "예" 를 누르십시오. 그러나 화면의 모든 메시지를 읽으십시오.
Security Breach Monitoring 이 (가) 귀하의 기기에 설치되었습니다. 즐겨!
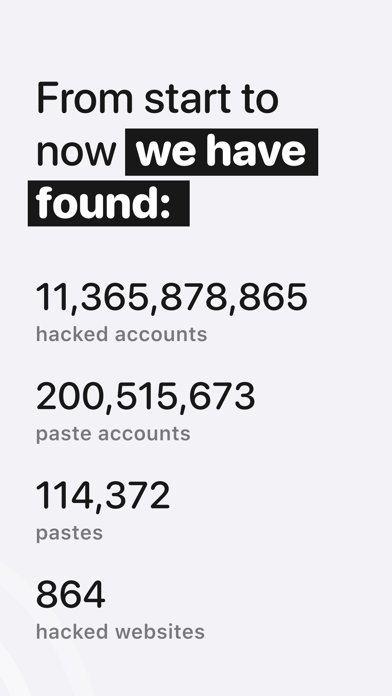
Hicy — is a data breach search & notification app that monitors online data leaks for user's security. Hicy aggregates data that's been exposed publicly and enables individuals to assess their exposure. ◆ How does it work? Searches only require an email address and provide immediate feedback. The notification service monitors for ongoing exposure and notifies an address owner if it subsequently turns up in a data breach. ◆ What exactly is a data breach? A data breach happens when personal or private information gets exposed, stolen, or copied without permission. These security incidents can be a result of cyber attacks on websites, apps, or any database where people's personal information resides. ◆ Why am I in this breach? Hackers often target massive companies with millions of users to get as much personal information and credentials as they can. These hackers look for a security weakness — the digital equivalent of leaving a door unlocked or window open. ◆ What information gets exposed in data breaches? Many data breaches expose email addresses and passwords. Others expose more sensitive information such as credit card numbers, passport numbers, and social security numbers. ◆ Do I need to be worried if my information gets exposed during a data breach? You should take steps to protect your personal information and accounts. If your password and email address get exposed, hackers can sell that information on the dark web to the highest bidder. Terms of Use: https://telegra.ph/Hicy-App--Terms-of-Use-05-29 Privacy Policy: https://telegra.ph/Hicy-App--Privacy-Policy-05-29 Hicy — is a data breach search & notification app that monitors online data leaks for user's security. Hicy aggregates data that's been exposed publicly and enables individuals to assess their exposure. ◆ How does it work? Searches only require an email address and provide immediate feedback. The notification service monitors for ongoing exposure and notifies an address owner if it subsequently turns up in a data breach. ◆ What exactly is a data breach? A data breach happens when personal or private information gets exposed, stolen, or copied without permission. These security incidents can be a result of cyber attacks on websites, apps, or any database where people's personal information resides. ◆ Why am I in this breach? Hackers often target massive companies with millions of users to get as much personal information and credentials as they can. These hackers look for a security weakness — the digital equivalent of leaving a door unlocked or window open. ◆ What information gets exposed in data breaches? Many data breaches expose email addresses and passwords. Others expose more sensitive information such as credit card numbers, passport numbers, and social security numbers. ◆ Do I need to be worried if my information gets exposed during a data breach? You should take steps to protect your personal information and accounts. If your password and email address get exposed, hackers can sell that information on the dark web to the highest bidder. Terms of Use: https://telegra.ph/Hicy-App--Terms-of-Use-05-29 Privacy Policy: https://telegra.ph/Hicy-App--Privacy-Policy-05-29